Your initial configuration on PA firewall may use MGT interface to access external services such as DNS server, content updates, and license retrieval. If you do not want to enable external network access to your management network, you must set up an in-band data port to provide access to required external services. This article shows how to do so.
1. Login to the web interface, for example https://192.168.11.11
2. Delete default virtual wire interface.
The PA firewall comes preconfigured with a default virtual wire interface between ports Ethernet 1/1 and Ethernet 1/2 (and a corresponding default security policy and zones). We will delete them.
* Delete the default security policy by selecting Policies>Security, select the rule, and click Delete
* Delete the default virtual wire, select Network>Virtual Wires by selecting the virtual wire and click Delete
* Delete the default trust and untrust zones, select Network>Zones by selecting each zone and click Delete.
* Delete the interface configurations, select Network>Interfaces and then select each interface (ethernet1/1 and ethernet1/2) and click Delete.
* Commit the changes
3. Configure the interface for external access to management services.
* Select Network>Interfaces>Ethernet and then the interface that corresponds to the port you want to use to access external services, ethernet1/1 in our example.
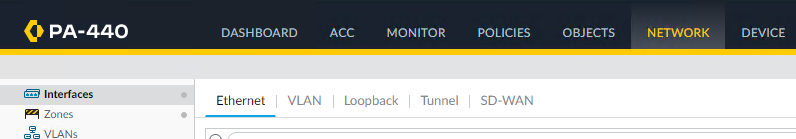
* Select the Interface Type, Layer3 in our example.
* In the Config tab, expand the Security Zone drop-down and select New Zone.
* In the Zone dialog, enter a Name for new zone, for example untrust, and then click OK.
* Select the IPv4 tab, select the Static radio button, and click Add in the IP section.
* Enter the IP address and network mask to assign to the interface, for example 192.168.11.12/24.
* Select Advanced>Other Info, expand the Management Profile drop-down, and select New Management Profile.
•A Name for the profile, such as Managing, and then select the services you want to allow on the interface.
•Note: in most cases, you probably only need to enable Ping.
•Click OK.
* To save the interface configuration, and then Commit.
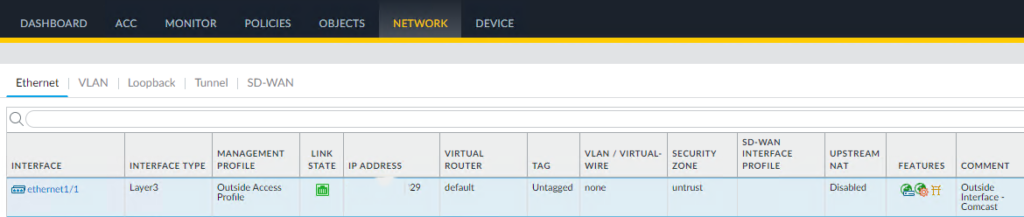
4. Configure the service routes such as DNS, Palo Alto Networks Services, URL Updates, and AutoFocus – this is option only if you don’t want to use Management profile.
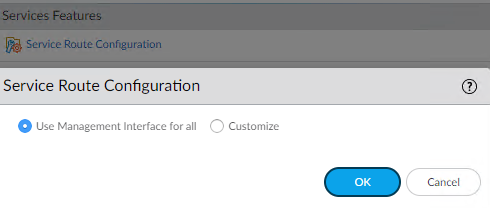
• Select Device > Setup > Services and click Service Route Configuration.
• Click Service Route Configuration
• Check DNS, Palo Alto Networks Services, URL Updates, and AutoFocus.
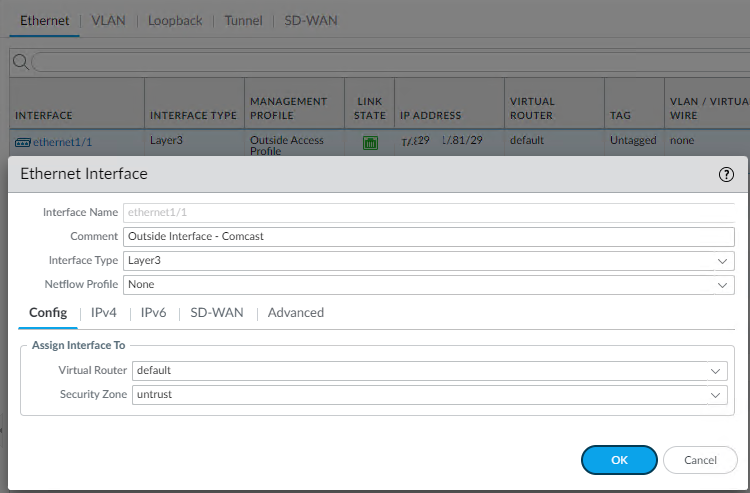
5. Configure an external-facing interface and an associated zone.
•Select Network>Interfaces and then select the external-facing interface, ethernet1/1 in our example.
•Select Layer3 as the Interface Type
•On the Config tab, create the associated Security Zone, such as untrust.
- Click on IPv4 and add the IP address
• Close the interface configuration and it looks like this.
6. Create a security policy rule to allow the firewall to send service requests from the internal zone to the external zone, Trust to Internet in our example.
7. To save the configuration, click on Commit.
8. Test by accessing Update Server Connectivity
•Select Device>Troubleshooting
•Select Update Server from the Select Test drop-down.
•Execute the Palo Alto Networks Update Server connectivity test.
* Also Access the firewall CLI, and use the following command to retrieve information on the support entitlement for the firewall from the Palo Alto Networks update server:
request support check
* If the configuration is correct, the update server will respond with the support status for your firewall. Because your firewall is not registered, the update server will return the following message:
If you have connectivity, the update server will respond with the support status for your firewall. Because your firewall is not registered, the update server will return the following message:
Contact Us
https://www.paloaltonetworks.com/company/contact-us.html
Support Home
https://www.paloaltonetworks.com/support/tabs/overview.html
Device not found on this update server
Please view this step by step video: